Tor:
Most likely you are accessing this website because you had some issue with the traffic coming from this IP/hostname. This router is part of the OnionMail Network into the Tor network, which is dedicated to providing privacy to people who need it most: average computer users.
Tor sees use by many important segments of the population, including whistle blowers, journalists, Chinese dissidents skirting the Great Firewall and oppressive censorship, abuse victims, stalker targets, the US military, and law enforcement, just to name a few. While Tor is not designed for malicious computer users, it is true that they can use the network for malicious ends. In reality however, the actual amount of abuse is quite low. This is largely because criminals and hackers have significantly better access to privacy and anonymity than do the regular users whom they prey upon. Criminals can and do build, sell, and trade far larger and more powerful networks than Tor on a daily basis. Thus, in the mind of this operator, the social need for easily accessible censorship-resistant private, anonymous communication trumps the risk of unskilled bad actors, who are almost always more easily uncovered by traditional police work than by extensive monitoring and surveillance anyway.
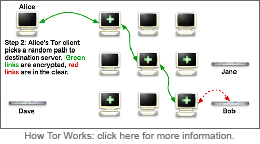
In terms of applicable law, the best way to understand Tor is to consider it a network of routers operating as common carriers, much like the Internet backbone. However, unlike the Internet backbone routers, Tor routers explicitly do not contain identifiable routing information about the source of a packet, and no single Tor node can determine both the origin and destination of a given transmission.
As such, there is little the operator of this router can do to help you track the connection further. This router maintains no logs of any of the Tor traffic, so there is little that can be done to trace either legitimate or illegitimate traffic (or to filter one from the other). Attempts to seize this router will accomplish nothing.
Furthermore, this machine also serves as a carrier of email, which means that its contents are further protected under the ECPA. 18 USC 2707 explicitly allows for civil remedies ($1000/account plus legal fees) in the event of a seizure executed without good faith or probable cause (it should be clear at this point that traffic with an originating IP address of onionmail.info should not constitute probable cause to seize the machine). Similar considerations exist for 1st amendment content on this machine.
If you are a representative of a company who feels that this router is being used to violate the DMCA, please be aware that this machine does not host or contain any illegal content. Also be aware that network infrastructure maintainers are not liable for the type of content that passes over their equipment, in accordance with DMCA "safe harbor" provisions. In other words, you will have just as much luck sending a takedown notice to the Internet backbone providers. Please consult EFF's prepared response for more information on this matter.
For more information, please consult the following documentation:
That being said, if you still have a complaint about the router, you may email the maintainer. If complaints are related to a particular service that is being abused, I will consider removing that service from my exit policy, which would prevent my router from allowing that traffic to exit through it. I can only do this on an IP+destination port basis, however. Common P2P ports are already blocked.
You also have the option of blocking this IP address and others on the Tor network if you so desire. The Tor project provides a web service to fetch a list of all IP addresses of Tor exit nodes that allow exiting to a specified IP:port combination, and an official DNSRBL is also available to determine if a given IP address is actually a Tor exit server. Please be considerate when using these options. It would be unfortunate to deny all Tor users access to your site indefinitely simply because of a few bad apples.

OnionMail is an open source mail router between tor network and internet. OnionMail uses filesystem with strong cryptography and some extended functions. This server also allows you to use the email in the tor network without losing the ability to communicate with the Internet.
Dealing with unwanted messages with X-Notice headers:
In the eventuality of unwanted messages with X-Notice headers, contact the SysOp immediately.
You can always contact him at these addresses:
Within the Internet: You can find the address in the X-Notice header. It usually is in the form sysop.xyz.onion@domain.tld
where xyz.onion is the OnionMail server and domain.ltd is an internet address of the entry node Within Tor:
sysop@xyz.onion
OWNERS AND/OR ADMINISTRATORS OF THE ENTRY/EXIT NODE CANNOT BE HELD RESPONSIBLE FOR ROUTING AND FOR THE MESSAGES BEING SENT. THIS IS BECAUSE THE USER CAN SELECT MULTIPLE EXIT NODES AND HENCE CHANGE THE ADDRESS AFTER THE "@" CHARACTER WITHOUT THE EXIT NODE'S SYSOP KNOWING.
Therefore, it's better to warn the .onion server's administrator with a simple email. You can also ask the node's administrator to be put in the exit policy.
This way, the node won't be able to send or receive messages from your server or address.
How is made the routing:
The mail addresses coming out here have this syntax:This server removes the part after the character "@" and put the character "@" before the Tor network's address, then send the message via tor network.username.toraddress00000.onion@domain.tldWhen an email is going form the Tor network to the Internet , this server replace the character "@" with a dot "." and append at the end of the address a character "@" and the domain name of the server, then send the message via Internet.username@toraddress00000.onion
V.M.A.T. and normal e-mail addresses:
When a VMAT addres is registered by the user the mail address appear to be a normal Internet mail address (in the TOR network and in the Internet).Mail transport overview:
To get informations about the server see the X-VMAT headers. From OnionMail 1.4 the users can register a VMAT (Virtual Mail Address Translation) that change the message routing to the real OnionMail SMTP server.The VMAT address is an alias used to connect the SMTP server directly without message reprocessing. See the RULEZ file to get more details.
All OnionMail server are connected in a federated network to check the SSL certificates and working state. All federated server can connect to the Internet via exit/enter servers to forward messages between networks.
OnionMail through the exit/enter nodes forwards messages between networks TOR and internet in a transparent manner.
Internet =? TOR
TOR =? Internet
How to get more information:
OnionMail servers security:
OnionMail uses filesystem with strong cryptography and asymmetric keys. Allusers use GPG mail encryption. All cryptographic keys of the server are not into the server. All keys is sored in a tor cloud network and all keys are calculated via F(X) by other OnionMail servers. The autodestruction certificate can delete all F(X) seeds without access to the original server. Some trusted network check the SSL certificates and the servers security and identity.
All systems are safe even in the event of theft, damage, tapping, tampering, also generating the appropriate alerts to users.
It is possible that the server in question is not actually an OnionMail server, but it can be a router of the NTU project.